v2.0.1-final
Securing Your Cluster
Security should never be an afterthought in Kubernetes. The default settings are often too permissive for a production environment.
- RBAC (Role-Based Access Control): Follow the principle of least privilege. Only grant permissions that are absolutely necessary.
- Network Policies: By default, all pods can talk to each other. Use Network Policies to restrict traffic and isolate sensitive workloads.
- Image Scanning: Scan your container images for vulnerabilities before deploying them. Tools like Trivy or Clair can be integrated into your CI/CD pipeline.
Resource Management
One of the most common causes of instability in Kubernetes is poor resource management. Always set requests and limits for your containers.
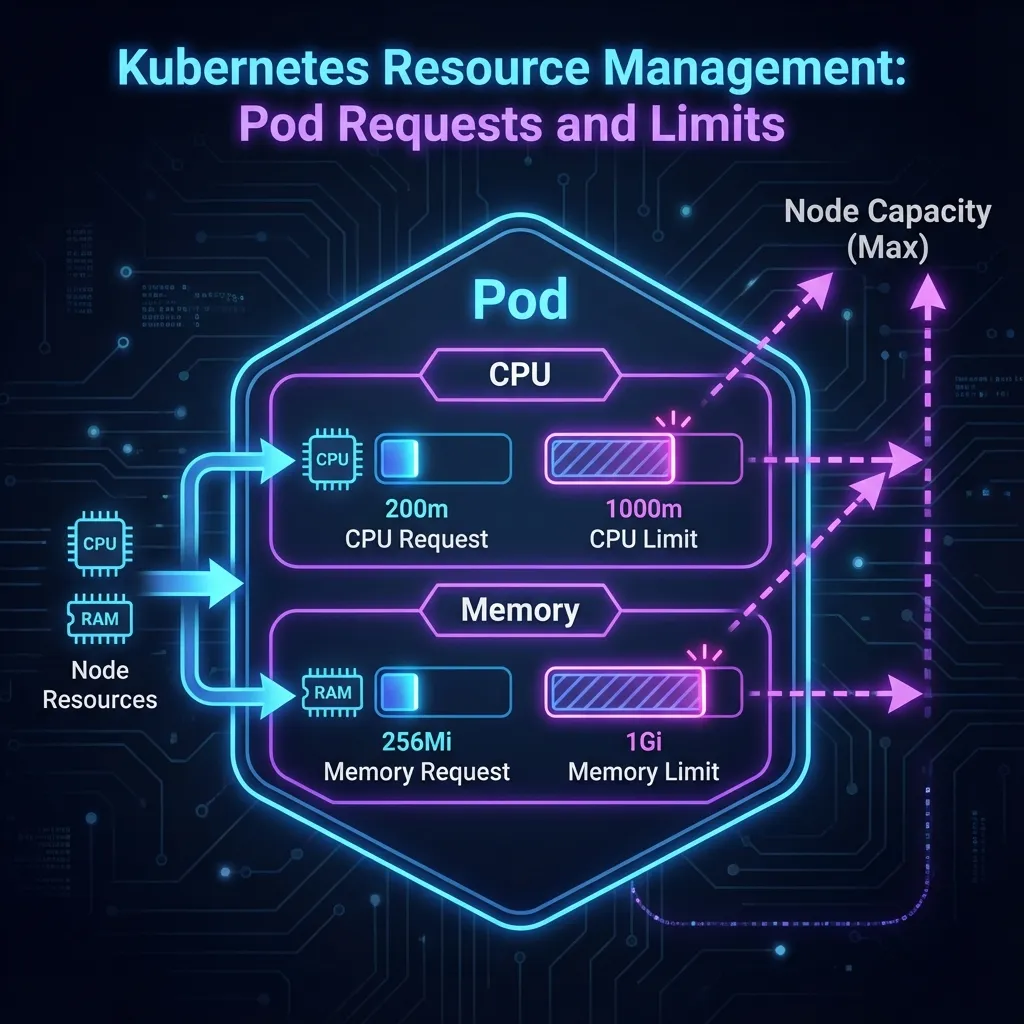
resources:
requests:
cpu: 100m
memory: 128Mi
limits:
cpu: 200m
memory: 256MiRequests guarantee that a pod gets the resources it needs, while Limits prevent a single pod from starving the entire node. Be careful with CPU limits, as they can cause throttling, but memory limits are essential to prevent OOMKilled errors.
Observability
You can't fix what you can't see. Monitoring and logging are crucial for understanding the health of your cluster.
- Metrics: Prometheus and Grafana are the industry standard for collecting and visualizing metrics.
- Logs: Use a centralized logging solution like ELK Stack (Elasticsearch, Logstash, Kibana) or Fluentd to aggregate logs from all pods.
- Tracing: Implement distributed tracing (e.g., Jaeger or OpenTelemetry) to debug complex microservices interactions.
